Center for Internet Security (CIS) – Healthcare Cybersecurity Challenges during the COVID-19 Pandemic
Healthcare organizations continue to be targets for adversaries, especially during the global COVID-19 pandemic. Cybersecurity often takes a backseat to patient care as organizations are struggling to keep up with the unprecedented demand on services and requirements for IT infrastructure expansions to accommodate telehealth and other new initiatives. Cyber-criminals are capitalizing on this reality and using phishing campaigns, ransomware, and other targeted attacks against healthcare organizations while they are most vulnerable.
The COVID-19 pandemic forced a majority of organizations to quickly pivot in order to continue services. A large number of employees are now working from home and medical offices moved to telehealth appointments. Cloud-based meeting and connectivity services such as Zoom, WebEx, Microsoft 365, Google, and others were purchased and implemented quickly – often without all the security checks and testing that an organization would normally undertake.
All of this has created a number of new threats that many organizations have not been prepared to address. For example, organizations that traditionally had IT resources in their own data center and all of their IT security protecting their own network perimeter are finding little protection available for their employees working from home. Other organizations are finding comingled data being stored in the cloud without the appropriate security and privacy controls in place, leading to unauthorized access by both insider threats and external attackers.
IT departments are struggling to deploy security updates and patches to systems deployed at users’ homes. Equally as challenging is remotely controlling, monitoring, and scanning distributed systems. This often leads to cybersecurity organizations being blind to alerts and notifications as well as the vulnerabilities present on distributed systems.
This reduction in visibility has allowed attackers to compromise systems without being noticed, potentially resulting in deployment of malicious software such as ransomware, locking critical systems and data until a ransom is paid. Ransomware attacks against U.S. healthcare organizations is specifically increasing since COVID-19.
Defense in Depth for Hospital Cybersecurity
In the face of the COVID-19 related challenges presented by a remote workforce, rapid change, and expanded ransomware attacks on U.S. hospitals, the Center for Internet Security® (CIS®) is helping U.S. hospitals defend themselves with several free tools, which all add up to a defense in depth approach to cybersecurity.
CIS is a community-driven non-profit, responsible for the globally recognized CIS Controls and CIS Benchmarks security best practices. These help organizations reduce risk and attack surface and are mapped to or referenced by common industry security frameworks such as HIPAA, NIST, and ISO. Additionally, CIS is home to the Multi-State Information Sharing and Analysis Center® (MS-ISAC®), the trusted resource for cyber threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial (SLTT) government entities, including public hospitals and healthcare systems. Teams of cybersecurity professionals are working 24x7x365 combatting real-time attacks that members, including healthcare providers, are experiencing.
CIS’s defense in depth approach to cybersecurity starts with prevention through our best practices, and continues through our operational technology and service offerings. The best practices are available for any organization to download from cisecurity.org at no cost. Eligible public organizations can also join the MS-ISAC at no cost to take advantage of many of the operational security technologies and services.

CIS Introduces Free Ransomware Protection Service for U.S. Hospitals
While public hospitals have long been eligible for cybersecurity resources from the MS-ISAC, there was a gap in support for private hospitals. This year, the CIS Board of Directors expanded the organization’s operational mission of making the connected world a safer place to help secure U.S. hospitals – both public and private – from the increased threat of cyber-attacks brought on hospitals by the COVID-19 pandemic.
In February 2021 it was announced that CIS is fully funding the Malicious Domain Blocking and Reporting (MDBR) service for all U.S. private hospitals. The service has been available for all public hospitals, health departments, and healthcare organizations through the MS-ISAC since July 2020. MS-ISAC funding for public hospitals is provided by the U.S. Department of Homeland Security’s (DHS) Cybersecurity & Infrastructure Security Agency (CISA).
The MDBR service is particularly effective against the threat of ransomware. Ransomware has emerged as the largest cyber threat facing hospitals today, especially since the onset of the COVID-19 pandemic. Ransoms demanded from cybercriminals to unlock systems and files have exceeded millions of dollars. In some cases, patient care has even been delayed or cancelled due to locked-out digital medical records and treatment regimens.
More than 1,500 U.S. SLTT organizations have already been using the MDBR service. It usually takes less than 5 minutes to configure. The service redirects any requests for internet domain names, checking to ensure any link clicked or web address browsed to is safe. MDBR proactively blocks any attempt to access a malicious domain, saving organizations from various attacks including phishing, malware, and ransomware.
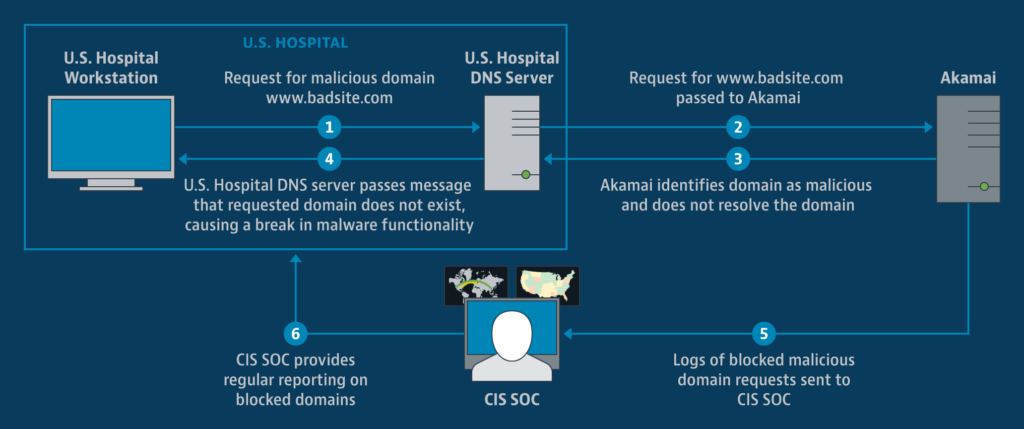
The MDBR service has blocked 127,888 requests to malicious domains for just healthcare organizations so far this year. Any of those requests could have resulted in a compromise resulting in the loss of confidentiality, integrity, or availability of healthcare systems and/or data.
A History of Mission-focused Cybersecurity
CIS has a long history in cybersecurity. The non-profit was founded in August 2000, when a group of business and government leaders met to discuss the rising threats of cyberattacks and their impacts on small- and medium-sized organizations. Twenty years later the outcome of that meeting is an independent, mission-driven, non-profit focused on preventing and mitigating the world’s most sophisticated cyber threats. CIS has built a global community of cybersecurity experts to help develop the best practice recommendations found in the CIS Controls and CIS Benchmarks.
The MS-ISAC became part of CIS in 2010, helping U.S. SLTT organizations operationalize and strengthen their cybersecurity. This is especially meaningful for those smaller SLTT organizations that may have little or no talent and funding focused on cybersecurity.
Combining the insights from a global community of cybersecurity experts with near-real-time operational insights provides CIS with tremendous visibility into both the threat landscape organizations face and innovations to combat those threats.
Looking Forward for Healthcare Cybersecurity
With 2021 being eventful right from the start in terms of ransomware attacks, CIS is doubling down on offering U.S. hospitals defensive solutions like MDBR at no cost as part of the mission to make the connected world a safer place.
CIS is accomplishing its mission by helping hospitals stay focused on accomplishing theirs. There are approximately 6,500 hospitals across the U.S. and CIS is striving to get thousands of them signed up for the MDBR service within 2021. Protecting hospitals against ransomware and other threats is the right thing to do and CIS is uniquely suited to do it. CIS is fully funding the MDBR program for private U.S. hospitals at no cost, and with no strings attached.
Visit https://www.cisecurity.org/hospitals/ to learn more about the service and other ways CIS can help support better cybersecurity.
Acknowledgement: This material is based upon work supported by the U.S. Department of Homeland Security under Grant Award Number, (19PDMSI00002).
Disclaimer: The views and conclusions contained in this document are those of the authors and should not be interpreted as necessarily representing the official policies, either expressed or implied, of the U.S. Department of Homeland Security.